
Bridge the Gap to IIoT with AUTOSOL Bridge
Industrial organizations are increasingly adopting IIoT technologies to modernize their operations and leverage real-time data for better decision-making. However, many facilities...

AUTOSOL recently attended the 2025 Spring Committee on Petroleum Measurement Standards (COPM) Meeting in San Francisco, a critical gathering for the...
Read More
Industrial organizations are increasingly adopting IIoT technologies to modernize their operations and leverage real-time data for better decision-making. However, many facilities...

At AUTOSOL, we’re committed to empowering professionals across the industrial automation and data management landscape. With that in mind,...
In the rapidly evolving fields of oil and gas, as well as utilities, the integration of Machine Learning (ML)...

HSE Data Management with AUTOSOL: In the fast-paced world of Health, Safety, and Environmental (HSE) management, the ability to...

In the realm of Industrial Internet of Things (IIoT), seamless communication is paramount for efficient and reliable operations. One...

How AI, Cloud, Edge Computing, and Autonomous Control are Transforming Operations and How AUTOSOL’s eACM Platform Can Help The...

AUTOSOL is excited to announce the launch of the new internship program, AIM (Automation, Innovation, and Mastery) kicking off...
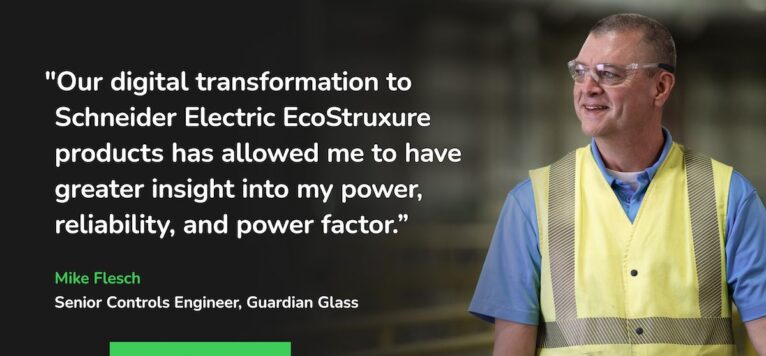
In a world that increasingly relies on data-driven decision-making, industries like oil and gas, water and wastewater management, and...

OPC stands for Open Platform Communication, and it is a set of standards developed by the OPC Foundation for...

The Southern Gas Association (SGA) recently hosted a powerful keynote panel, “Natural Gas Energy During an Evolving Time,” featuring Joe Hampton...

MQTT is a lightweight messaging protocol, which is widely used for IoT applications, thanks to its low overhead and...

Key benchmarks for identifying highly effective industrial data communications in today's data intensive realities.